You are here
Making TurnKey more turnkey - the end to default passwords
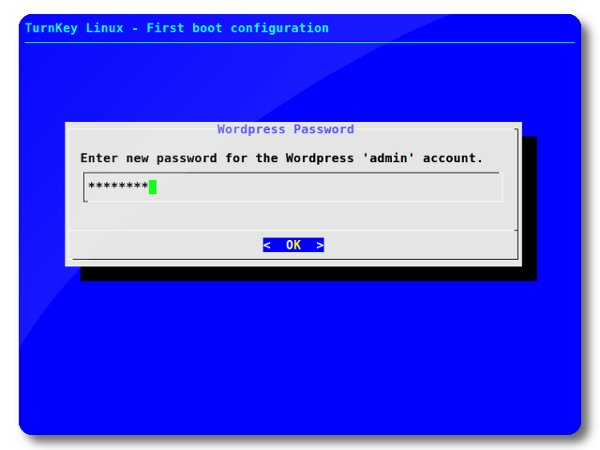
In our quest to make the upcoming TurnKey 11.0 release more "turnkey", I set out to extend the firstboot inithooks to include application specific configuration hooks such as setting of the admin password, email and domain to serve (where applicable).
I'm glad to announce that the quest is now over, and that puts the end to default passwords.
But what about hosting/cloud deployment where the user doesn't have boot interaction? Well, all the configurations can be pre-seeded. We'll be adding support for preseeding to the Hub soon after the 11.0 release. Until then, the instances will use default passwords, but they can be easily changed by executing the inithooks directly.
While on my quest, it was interesting to get a birds eye view of how the different applications store their passwords, so I thought I'd share:
Comparison table (22 applications)
| clear | crypt | md4 | md5 | sha1 | salt | |
| tomcat | x | |||||
| trac | x | |||||
| otrs | x | |||||
| twiki | x | |||||
| mldonkey | x | |||||
| joomla | x | |||||
| mantis | x | |||||
| wordpress | x | |||||
| dokuwiki | x | |||||
| phpbb | x | |||||
| extplorer | x | |||||
| gallery | x | x | ||||
| deki | x | x | ||||
| mediawiki | x | x | ||||
| moodle | x | x | ||||
| prestashop | x | x | ||||
| magento | x | x | ||||
| vtiger | x | x | ||||
| bugzilla | x | x | ||||
| roundup | x | |||||
| redmine | x | |||||
| django | x | x |
Foot notes
- clear: Passwords are stored in clear text.
- crypt: Passwords are hashed with crypt or htpasswd.
- md4/md5/sha1: Passwords are put through a cryptographic hash function, which is a deterministic one-way procedure that takes a block of data and returns a fixed-size bit string.
- salt: A salt (random bits) are added to the password before passing it through the hash function. Some of the applications use a randomly generated salt stored in a configuration file, others calculate it on the fly and add it the hash itself, while others use the user id as the salt. Using a salt is meant to add to the complexity and time it would take an attacker (who obtained the hashed passwords) to determine the original clear-text password.
Now for some code snippets
tomcat
doc = xml.dom.minidom.parse(TOMCAT_USERS).documentElement
users = doc.getElementsByTagName('user')
for user in users:
if not user.getAttribute('username') == 'admin':
continue
user.setAttribute('password', password)
trac
system("htpasswd -cb %s admin %s" % (authfile, password))
otrs
hashpass = crypt.crypt(password, 'ro') # 2 chars of username/email
twiki
output = getoutput("htpasswd -bn foo %s" % password)
hashpass = output.split(":")[1].strip()
mldonkey
MD4_HASH=$(echo -n $PASSWORD | openssl dgst -md4 | tr [a-z] [A-Z])
joomla
hashpass = hashlib.md5(password).hexdigest()
mantis
hashpass = hashlib.md5(password).hexdigest()
wordpress
hashpass = hashlib.md5(password).hexdigest()
dokuwiki
hashpass = hashlib.md5(password).hexdigest()
phpbb
hashpass = hashlib.md5(password).hexdigest()
extplorer
MD5_HASH=$(echo -n $PASSWORD | md5sum | cut -d " " -f 1)
hashpass = hashlib.md5(password).hexdigest()
gallery
salt = "".join(random.choice(string.letters) for line in range(4)) hashpass = salt + hashlib.md5(salt + password).hexdigest()
deki
hashpass = hashlib.md5(password).hexdigest()
hashpass = hashlib.md5("1-" + hashpass).hexdigest() # userid 1
mediawiki
hashpass = hashlib.md5(password).hexdigest()
hashpass = hashlib.md5("1-" + hashpass).hexdigest() # userid 1
moodle
for line in file(conffile).readlines():
m = re.match("\$CFG->passwordsaltmain = '(.*)';", line)
if m:
salt = m.group(1)
hashpass = hashlib.md5(password + salt).hexdigest()
prestashop
for line in file(conffile).readlines():
m = re.match("define\('_COOKIE_KEY_', '(.*)'", line)
if m:
cookie_key = m.group(1)
hashpass = hashlib.md5(cookie_key + password).hexdigest()
magento
salt = "".join(random.choice(string.letters) for line in range(2)) hashpass = hashlib.md5(salt + password).hexdigest() + ":" + salt
vtiger
hashpass = hashlib.md5(password).hexdigest() $salt = substr($username, 0, 2); $salt = '$1$' . str_pad($salt, 9, '0'); $encrypted_password = crypt($password, $salt);
bugzilla
$salt = '';
for ( my $i=0 ; $i < 8 ; ++$i ) {
$salt .= $saltchars[rand(64)];
}
$cryptedpassword = crypt($password, $salt);
roundup
hashpass = "{SHA}" + hashlib.sha1(password).hexdigest()
redmine
hashpass = hashlib.sha1(password).hexdigest()
django
salt = hashlib.sha1(str(random.random())).hexdigest()[:5] hash = hashlib.sha1(salt + password).hexdigest() hashpass = 'sha1$%s$%s' % (salt, hash)
Comments
Nice!
Excellent work guys, looking good, I like also that domains are being added where applicable. I'm anxiously waiting for the beta of the new appliances!
Thanks Adrian
It was a lot of work but I think it adds a lot to the user-experience and was worth the effort.
We'll be including Magento, PrestaShop and VTiger with the 11.0 release (coming shortly), as they are ready and no point in holding them back. I've also taken notes for feedback (for you and Basil) which I need to summarize - I'll try get that done soon.
Looking forward for your feedback
I'm sure I'll learn a couple of lessons from that feedback. I'v already learned a lot helping this project. BTW, I'm missing your feedback on the tklpatch commands of the tkldevenv. I'll upload the entire patch to github so that when you are finally free of the 11pt1 release, you can easily pull/diff those. As you are the author of the original scripts, your feedback is invaluable to the future of that appliance.
Good idea regarding github...
Good idea regarding github, that will make it a lot easier to pull the code. It should also make your life simpler publishing updates, and tracking revisions (which I hope you're already doing).
I'll push out the feedback as soon as I can.
Brilliant
This is brilliant. And knowing how to do that is magical and genious from my point of view. I'm trying to make sense of the code snippets and not getting very far. I understand when values are being passed to MySQL - but take Redmine for example: is that line a part of a configuration file, or is that the value of the field in the MySQL table? Fascinated.
Thanks Rik! The code snippets...
Thanks Rik!
The code snippets only show how we take the clear text password and convert it into the desired hash for storage. The code displayed in the post are (mainly) taken from the /usr/lib/inithooks/bin/$APP.py, which is called from the related script in firstboot.d (which may preseed the answers).
Why the separation of code? Unix philosophy - do one thing, and do it well. Take a look (if you haven't already) at the inithook documentation.
To wet your appetite (as you asked so nicely), I've attached the full bin/redmine.py
Alon, Thanks for taking the time
I know how busy you are and really fully appreciate that you took the time to lay some of this out for me. I'm working through Python in a class, and am gonna enjoy digging in see mechanism. Thanks again,
Rik
Briliant!
Very tidy feature!
TurnKey Hub updated to support 11.0 and preseeding
I've been asked via email, on twitter as well on the forums when the 11.0 release is coming out, and I promised before the end of the year. We partly lived up to my promise. All 11.0 ISO's have been released, TKLBAM profiles updated, and Amazon Images (AMI's) uploaded.
And now, before the new year comes in, I pushed out a large update to the Hub which adds:
We'll be making the official 11.0 announcement once the VM builds are ready and released, and in that announcement include more details on what has changed in the Hub.
Lastly, if you come across any issues with the Hub, please post a comment or send feedback via the Hub.
Question on importing "clear" passwords into Magento -> get hash
I am looking around the web for ways to import batches of customers into Magento and move cleartext passwords into hashed format.
I see your method for hashing the Admin password.
Is there a way, for instance in Open Office or MySQL to convert a clear password to the correct Hashed password?
The only other method I know it to tell customers they have been imported to the new system, and please follow the "lost password" link to set a new one. This is somewhat untidy it seems.
Thanks for all the great work. Awesome set of work here!
You can access your server vai webshell or webmin
You can access your server vai webshell or webmin
See http://www.turnkeylinux.org/core for port numbers and sample screenshots.
Cheers,
Tim (Managing Director - OnePressTech)
There is an issue with the Jenkins appliance.
See the bug report here and in the forums here (with a workaround). However AFAIK this shouldn't affect SSH login, so perhaps the non-US keyboard is also a culpret...
My suggestion would be to either install with a US keyboard (if you have one) and then change the keyboard to whatever you are using. Or just use a very simple password initially (with keys that will work...), configure your non-US keyboard and then reset the password. I don't have instructions handy on how to set up your non-US keyboard but google should get you going, just keep in mind that TKL v12.x is based on Debian Squeeze...
Also FWIW I have run a poll to ask about setting timezone and/or non-US keyboard on first boot. It is also logged on the TKL Dev traker. There is also a bug report about non-US keyboard causing log in issues (although this seems to be mainly from the web browser).
Perhaps post on that thread?
I am all out of ideas and have no experience with Jenkins. Perhaps someone on that thread has some further ideas for you?
Pages
Add new comment